
Your chance to shape the proposed SOCI Act Risk Management Program Rules

Draft rules which will switch on obligations relating to Critical Infrastructure Risk Management Programs under the SOCI Act are now open for consultation.
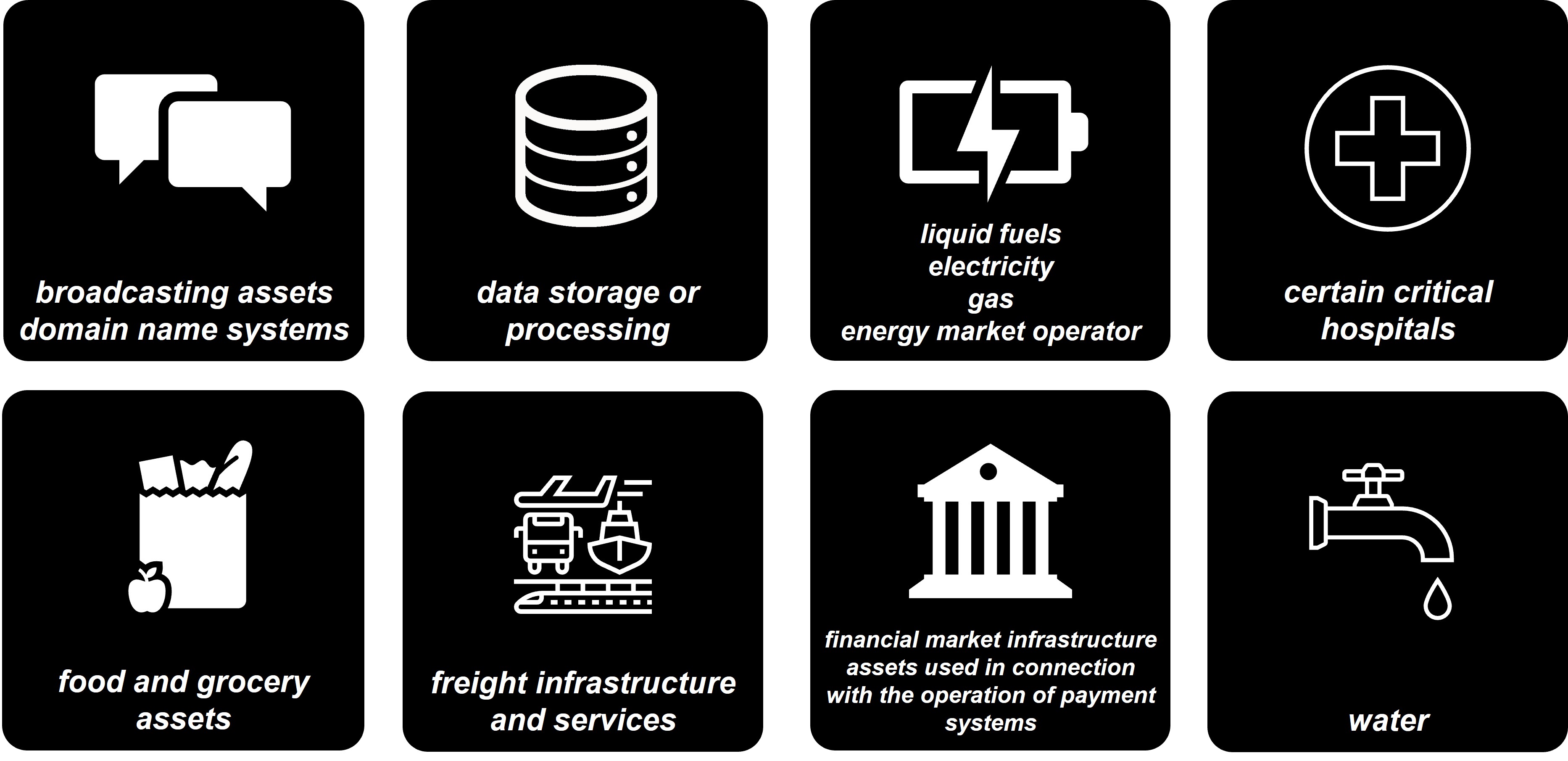
The Minister for Home Affairs has issued, for consultation, draft Risk Management Program (RMP) requirements under the Security of Critical Infrastructure Act (Cth) 2018 (SOCI Act). Part 2A of the SOCI Act requires entities to adopt and maintain an RMP in relation to their critical infrastructure assets. Once the draft Security of Critical Infrastructure (Critical infrastructure risk management program) Rules (LIN 22/018) 2022 come into effect, RMP obligations under the SOCI Act will be switched on.
The draft Rules propose:
- responsible entities will be required to plan for a range of hazards relating to physical and technical security, personnel and supply chain issues and natural hazards; and
- entities must adopt an independent IT security standard or equivalent framework (such as ISO 27001 or the Australian Cyber Security Centre’s Essential Eight Maturity Model.
Organisations impacted by the Rules should consider making a submission or participating in virtual town hall events.
Application of RMP Rules
What is a Risk Management Plan (RMP)?
An RMP is a written program with the purpose of:
- identifying each hazard where there is a material risk that the occurrence of the hazard could have a relevant impact on the relevant critical infrastructure assets; and
- so far as it is reasonably practicable to do so:
- minimising or eliminating any material risk of such a hazard occurring; and
- mitigating the impacts of such hazards on the relevant infrastructure critical assets.
The draft Rules require responsible entities to consider and plan for risks across four key domains:
- cyber and information security hazards;
- personnel hazards;
- supply chain hazards; and
- physical security and natural hazards.
A hazard will be considered to create a “material risk” of having a relevant impact on a critical infrastructure asset if the hazard may result in:
- impairment of the asset that may prejudice the social or economic stability of Australia or its people, the defence of Australia or national security;
- a stoppage or major slowdown of the asset’s function for an unmanageable period;
- a substantive loss of access to, or deliberate or accidental manipulation of, a critical component of the asset;
- an interference with the asset’s operation technology or information communication technology essential to the functioning of the asset;
- an impact resulting from the storage, transmission or processing of sensitive operational information outside Australia;
- an impact on the asset resulting from remote access to operational control or operational monitoring systems of the asset; or
- any other material risks as identified by the entity that affect the functioning of the asset.
RMP obligations
Cyber and information security hazards
For cyber and information security hazards, the Rules require that an RMP specify how the responsible entity will comply with at least one of the following standards and frameworks:
- Australian Standards AS ISO/IEC 27001:2015;
- the Australian Signals Directorate’s Essential Eight Maturity Model at Maturity Level One;
- the National Institute of Standards and Technology of the United States of America Framework for Improving Critical Infrastructure Cybersecurity;
- the Cybersecurity Capability Maturity Model by the Department of Energy of the United States of America (at Maturity Indicator Level 1);
- the 2020-21 Australian Energy Sector Cyber Security Framework Core by the Australian Energy Market Operator Limited at Security Profile 1; or
- a framework equivalent to any of the above.
Personnel hazards
A “responsible entity” must establish an RMP that identifies critical workers, assesses the suitability of a critical worker to have access to the critical components of the asset, and minimise or eliminate material risks relating to negligent employees, malicious insiders and off-boarding process. The assessment for suitability of a critical worker may include a background check under the AusCheck scheme.
Supply chain
An RMP must also minimise or eliminate a material risk of, or mitigate, the relevant impact relating to the “responsible entity’s” supply chain, including (among other things) threats to intellectual property within supply chain and high-risk vendors.
Physical security hazards and natural hazards
Finally, an RMP must minimise or eliminate a material risk of, or mitigate, the relevant impact of a physical security hazard on a critical site (which may include a data centre), which includes (among other things) identifying a critical site, controlling access to a critical site and testing security arrangements for the asset.
These requirements are likely to mean a significant uplift in security compliance for many organisations – particularly across industries previously outside of the scope of the SOCI Act.
Implementation timeframes and the RMPs
Once the Rules commence, the responsible entities for critical infrastructure assets must develop an RMP. Such entities should also be considering how to minimise risks of hazards occurring and mitigate any consequences should they occur.
From the date that is six months after the Rules are switched on, the responsible entity for a critical infrastructure asset must have in place and comply with an RMP which meets the requirements of the Rules.
However, the requirement for RMPs to specify how the responsible entity will comply with an independent cyber-security standard (or equivalent standard or framework) will only take effect within 18 months after the Rules are switched on, allowing entities further time to comply with this particular aspect of the Rules.
Penalties for non-compliance
Fines of $44,400 apply for each contravention of the requirements in relation to RMPs (including a failure to have an RMP, a failure to comply with an RMP, a failure to review an RMP on a regular basis and a failure to update an RMP).
Preparing for more switched on critical infrastructure assets
The Minister is currently accepting submissions in relation to the draft Rules from impacted entities, with consultation to end on Friday 18 November 2022. The Cyber and Infrastructure Security Centre (CISC) will be holding various Q&A sessions during the consultation period, with CISC staff available for meetings throughout.
If you own or operate (or potentially own or operate) critical infrastructure assets, you should:
- consider making a submission or attending virtual consultations held by the CISC;
- review your existing risk management plans and conduct a gap analysis against the draft Rules to confirm whether changes are required to achieve compliance; and
- identify any material risks within the four key domains of: cyber and information security, personnel hazards, supply chains, and physical security hazards and natural hazards and consider options to minimise the risks and mitigate their impacts.
Get in touch
